Our approach
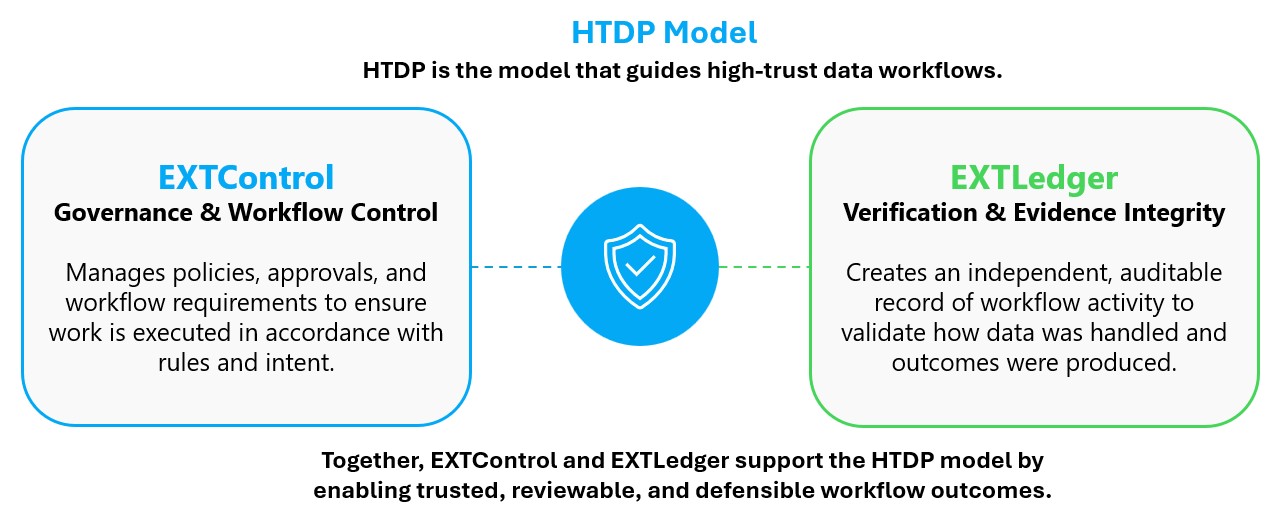
High-Trust Data Processing (HTDP)
A practical approach to building trust into data workflows.
High-Trust Data Processing is Zavenia’s approach to designing workflows where sensitive activity must be visible, auditable, and verifiable after the fact.
The model is built on a simple idea: trust should not rely on only policy, assumption, or explanation. In high-trust environments, critical workflow activity should remail traceable and reviewable after execution.
Zavenia develops technologies that support this approach, including EXTLedger, a verification and integrity layer for audit-ready data workflows, and EXTControl, a governance and control layer for enforcing workflow requirements.
Together, these technologies help organizations strengthen oversight, reduce evidence gaps, and increase confidence in how sentitive data is handles acrss complex environments.
HDTP Principles
1. Verifiable Activity
Critical actions in a workflow should be capable of independent review and validation.
2. Traceable Workflows
Data movement, transformations, approvals, and outputs should remain traceable and reviewable after execution.
3. Evidence Integrity
Workflow evidence should remain resistant to silent modification or loss over time.
4. Non-Distruptive Integration
High-Trust capabilities should operate alongside existing systems without replacing operational workflows.
5. Defensible Outcomes
Organizations should be able to demonstrate not only what was produced, but how it was produced.
Proprietary Technology
EXTLedger
Moving systems from assumed trust to verifiable trust.
EXTLedger is a verification and integrity layer designed for systems that require confidence in how data is handled, processed, and shared. It creates a persistent, auditable record of data activity, enabling validation of outcomes and traceability.
Rather than replacing existing systems, EXTLedger fits alongside data workflows to strengthen accountability, reduce evidence gaps, and support traceable data activity across complex environments.
It is designed for high-trust use cases across research, defense, and regulated systems where auditability, verification, and traceability are critical.
EXTLedger shifts data workflows from implicit trust models to verifiable ones, where critical workflow activity can be independently reviewed and validated. This provides end-to-end visibility across workflows, reduces reliance on assumptions, and strengthens oversight, particularly in environments where errors or manipulation carry significant risk.
EXTLedger Overview
Type:
Verification & Integrity Layer
Integration:
Non-disruptive, integrates into existing systems and workflows
Primary Function:
Validate how data is handled and ensure outcomes can be trusted
Output:
Auditable records and independently verifiable outcomes
Use Cases:
Research, Defense, Regulated Systems
Trust Model:
Supports internal validation and optional external verification
EXTLedger supports Zero Trust, CMMC, and ISO-aligned environments by strengthening workflow traceability, audit integrity, and independently verifiable evidence records. It helps organizations demonstrate how sensitive data was handled, transferred, and processed across complex operational workflows.
Core Capabilities
Verifiable Data Integrity
Ensure data and outcomes can be trusted and independently validated
Auditable Processing
Maintain a clear, traceable record of data handling and transformation
Operational Transparency
Provide clear visibility into how data moves through workflows and operational processes.
Optional Distributed Verification (XRPL)
Extend verification to a decentralized ledger, enabling independent and tamper-resistant validation across external parties
Where It Fits
Research & Scientific Environments
Support controlled data use and verifiable outcomes across research workflows
Defense & High-Security Systems
Enable trusted data handling and validation in mission-critical environments
Regulated Industries
Maintain auditability and confidence in sensitive data workflows across compliance-driven systems
High-Trust Operational Systems
Ensure outcomes can be trusted and independently verified in complex environments
Applied Systems
Systems built and tested in environments where trust cannot be assumed and outcomes must be verified.
IMPACT LAB
From Technical Failure to Care Impact
Simulated failure scenarios in lab result delivery workflows to evaluate latency, system breakdowns, and downstream patient impact.
Why This Work Matters
These implementations reflect work in environments where assumptions break down, where data must be controlled, processing must be auditable, and outcomes must be independently verified.
SECURE HEALTHCARE
DATA ARCHITECTURE
Tokenization, Access Control & Blockchain-Anchored Audit Integrity
Designed secure, access-controlled data workflows with verifiable audit integrity.
EXT Ledger
Verifiable, Auditable Data Integrity For High-Trust Environments
Designed for evolving cryptographic standards and future-ready verification
Build With Zavenia
For organizations working on sensitive data, secure architectures, or high-trust systems, Zavenia develops focused technologies and applied prototypes that move complex ideas toward working solutions